Understanding the Importance of Authentication
Hey there, tech-savvy folks! In this digital age, where our lives are becoming increasingly intertwined with the online world, it’s crucial to talk about one of the unsung heroes of the digital realm: Authentication. I know, it might sound like a fancy term, but it’s your best buddy in keeping your digital life safe and sound.
What’s Authentication, Anyway?
Authentication is like the bouncer outside a nightclub, making sure only the right people get in. In the digital world, it’s a process that confirms your identity, proving that you are who you claim to be. You use it every day, whether you’re unlocking your smartphone, logging into your email, or accessing your bank account online.
Why is it So Darn Important?
- User Verification: First and foremost, it’s about making sure that you are who you say you are. Imagine if just anyone could waltz into your email or social media accounts – chaos, right?
- Guarding Your Data: We all have stuff we want to keep private, like family photos or personal messages. Authentication ensures that only you and those you trust can access these precious digital bits.
- Access Control: Think of this as the VIP section of a club. Authentication lets you decide who gets into your private corner of the digital world. You control who sees what.
- Accountability: It’s like having a digital detective that keeps track of everything that happens. If anything goes wrong, you can trace it back to the source.
- Preventing Sneaky Intruders: Without authentication, anyone could potentially access your accounts or even manipulate your data. We don’t want that, do we?
- Double Trouble: Multi-Factor Authentication (MFA): This is your sidekick in the world of authentication. It’s like requiring two keys to unlock your treasure chest. MFA combines what you know (like a password) with something you have (like your phone) or something you are (like your fingerprint).
- Password Protection: Remember those pesky password requirements? They’re all part of the authentication game, making sure your passwords are tough nuts to crack.
- One-Stop Shopping: Single Sign-On (SSO): SSO lets you use one set of keys (credentials) to access multiple services. It’s like having a magic key that opens all the doors without needing a separate one for each.
- Playing by the Rules: Compliance: Many industries and organizations have rules about data security. Proper authentication helps meet these rules and keeps everyone on the right side of the law.
- Thwarting Cyberattacks: Cyberattackers are always looking for a way in. Authentication makes their job a lot harder. It’s like adding extra locks and a security system to your digital house.
In a nutshell, authentication is the unsung hero of our digital lives. It keeps our personal stuff personal, prevents unauthorized access, and is our first line of defense against cyber bad guys. So next time you’re prompted to enter your password, know that it’s not just a pesky step – it’s your digital bouncer, keeping your online world safe and sound. Don’t underestimate the importance of this digital superhero!
The Role of JWT Token-Based Authentication
What’s a JWT Token, Anyway?
JWT stands for “JSON Web Token” but let’s keep it simple. Think of it as a digital key, just like your trusty physical key unlocks your front door. This digital key, however, opens the doors to your favorite online services, like a secret handshake between you and your apps.
How Does It Work?
Here’s the cool part: JWT token for authentication is all about trust. When you log into a website or app, it hands you a token (your digital key) after you prove you’re you. This token is like a secret code, and it’s a compact piece of information that contains your identity.
Now, when you want to access a different part of the app or website, you show this token. It’s like saying, “Hey, I’m the same person who logged in a while ago.” The server believes you because it can decode the token and check if it’s valid. No need to keep typing your password everywhere – your token vouches for you!
Why JWT Token For Authentication Rocks:
- Security Superhero: JWT tokens are like Fort Knox for your digital life. They’re tamper-proof and encrypted, making it incredibly tough for cyber-villains to forge them.
- Speedy and Efficient: Traditional methods require constant back-and-forths with the server. But with JWT tokens, you log in once, get your token, and then zip around the app without repeatedly entering your password.
- Scalability: It’s the perfect sidekick for single sign-on (SSO). With one JWT token, you can access multiple services, making your digital life super convenient.
- Enhanced User Experience: No one likes remembering dozens of passwords. JWT tokens simplify your online existence, ensuring you don’t get locked out of your favorite platforms.
- Crossing Boundaries: JWT tokens are like global citizens. They can work seamlessly with different programming languages and platforms, ensuring compatibility and flexibility.
So, next time you log into your favorite app effortlessly, thank JWT for authentication. It’s the unsung hero ensuring your online journey is not just secure but also smooth and hassle-free. Cheers to digital convenience and security!
Common Problems and Challenges of JWT Token for Authentication
Hello there, fellow tech enthusiasts! We’ve all heard how JWT (JSON Web Tokens) are like the golden ticket to seamless authentication, right? But, like any superhero, even JWT has its quirks and challenges. Let’s explore the common problems and hiccups that can crop up in the world of JWT authentication.
1. Token Tampering:
Imagine your golden ticket to a theme park suddenly becomes a fake. Well, JWT tokens, although secure, can be tampered with. If a cyber-trickster gets hold of your token, it might change its data, which can lead to unauthorized access. Staying vigilant and protecting your tokens is key.
2. Lack of Revocation:
Once a JWT token is issued, it’s valid until it expires. There’s no easy way to revoke a JWT token before its expiry date. So, if you lose your token or it falls into the wrong hands, there’s no straightforward way to deactivate it. This can pose a challenge, especially in cases of lost or stolen tokens.
3. Token Size:
JWT tokens can grow in size as you add more claims (pieces of information) to them. This size can become a challenge when these tokens are passed between a client and a server, especially if you’re on a slow or unreliable network. It might slow down your app’s performance.
4. Stateless Nature:
JWT tokens are stateless, meaning they don’t require storing the session state on the server. While this is often an advantage, it can be challenging for apps that need to track user sessions for various reasons, like analytics or auditing.
5. Limited Data Synchronization:
Once a JWT token is issued, any changes in the user’s data (like permissions) are not reflected until the token expires or is reissued. This can lead to inconsistencies in authorization data.
6. Key Management:
JWT relies on public and private keys for security. Managing these keys securely can be a challenge, especially in large, complex systems. If keys are compromised, it could spell trouble for the entire authentication process.
7. Centralized Validation:
For JWT tokens to be validated, each service or application needs to have access to the same secret key or the public key of the token issuer. This centralized key management can be complex in decentralized systems.
Despite these hiccups, JWT authentication remains a popular and versatile choice in the digital realm. Awareness of these challenges and implementing best practices can help you harness the power of JWT while keeping these quirks at bay. So, while JWTs might have their share of challenges, they’re still a valuable tool in the world of authentication.
Keeping It Fresh: Handling JWT Token Expiry
Have you ever noticed how sometimes you have to log back into an app or website after a while? That’s often due to JWT token expiry, but fear not, it’s all about keeping your online world safe.
What’s JWT Token Expiry?
Think of JWT tokens as cookies – not the chocolate chip kind, but the digital ones. They have a shelf life, and when they expire, you need a fresh one. This adds an extra layer of security by making sure that if someone gets their hands on an old token, it won’t be any good for long.
Why Does It Matter?
- Security Boost: Expiring tokens minimize the window of opportunity for potential hackers. Even if they somehow grab an old token, it won’t work for long.
- Regular Re-authentication: Expiry ensures you periodically prove you’re you, which is essential for your online safety.
- Smooth User Experience: It may seem like a minor inconvenience, but re-logging in now and then helps keep your digital world running securely.
So, when your app asks you to log in again, know that it’s a small price to pay for a safer and more secure online experience. Your digital world thanks you for it!
Best Practices for JWT Token Expiration
- Short and Sweet: Keep token lifetimes as short as possible. Ideally, they should only last for minutes or hours, depending on the use case. This limits the window of opportunity for any potential security threats.
- Signature Seal: Like an official stamp, signatures on JWTs prove their authenticity. They ensure that nobody has meddled with your token on its way to and from the server. If the signature doesn’t match, it’s like a red flag waving – something’s not right.
- Regular Rotation: Like changing your toothbrush, it’s essential to regularly rotate your tokens. Use refresh tokens to issue new access tokens when they expire. This helps maintain security without requiring users to log in constantly.
- Never Trust the Client: Don’t rely solely on the client-side to protect your JWTs. The server should always be the one double-checking the token’s integrity.
- Grace Period: Implement a small grace period after token expiration. It’s like letting someone finish their ice cream before telling them it’s time to leave. This prevents abrupt access denials and offers a smooth user experience.
- Logging and Monitoring: Keep a vigilant eye on token expiration events. Log and monitor token activity to detect any unusual patterns or potential security breaches.
- User-Friendly Communication: When a token expires, communicate this clearly to the user. User-friendly error messages help users understand why they need to log in again.
- Customization: Tailor token expiration policies to match your application’s specific needs. Not all apps are the same, and your token lifetimes should reflect that.
So, remember, just like your favorite snacks, JWT tokens have an expiration date for a reason. Following these best practices ensures your digital world stays secure, and your users enjoy a seamless experience. It’s all about keeping things fresh and safe in the realm of digital security.
Navigating Performance Challenges with JWT Tokens: Keeping Your Digital Journey Smooth
While JWT (JSON Web Token) authentication is a fantastic tool, like any superhero, it has its kryptonite. Let’s chat about the performance challenges you might encounter on your digital adventure with JWT tokens.
1. Size Matters: JWT tokens can grow in size as you add more claims (data) to them. When these tokens become hefty, it can slow down your network, especially if you’re sending them with every request. Think of it as carrying a backpack filled with rocks while hiking – it’s going to slow you down!
2. No Revoking Powers: Once a JWT token is issued, it’s immutable. This means you can’t revoke it. So, if you need to log out as a user or change permissions, you’ll have to rely on the token’s expiration time. It’s like giving someone a lifetime pass to an event; you can’t take it back.
3. Security vs. Speed: The security of JWT tokens is their strong suit, but the process of validating and decoding them can be resource-intensive. Striking the right balance between security and performance can be a challenge.
4. Complexity Can Creep In: As your application grows, you might find yourself dealing with complex token management. This can lead to slower performance, increased maintenance, and debugging headaches.
5. Statelessness Trade-Off: JWT tokens are stateless, meaning they don’t rely on a server’s memory. While this is an advantage, it can lead to more database queries, potentially affecting performance.
But fear not! While these challenges exist, they can be tamed. Properly optimizing and managing your JWT tokens can keep your digital journey running smoothly. So, as you set out to harness the power of JWT tokens, be mindful of these potential hiccups and ensure they don’t trip you up on your quest for a seamless online experience.
Choosing the Right Web Authentication Method: Your Key to a Seamless Online Experience
You know that feeling when you’re faced with a bunch of doors, and you’ve got to pick the right key to unlock the one you want? Well, that’s what choosing a web authentication method is like. It’s about finding the perfect key for your online world. Let’s dive in!
Key Choices:
- Good Ol’ Passwords: Remembering passwords can be like juggling flaming torches. But they’re still the most common choice. Just make sure your password is strong and unique for each site to keep the digital burglars at bay.
- Biometrics – Say Cheese or Touch It: Fancy using your face, fingerprint, or even your iris to unlock your digital doors? Biometric authentication is like magic, but it depends on the device you’re using.
- Tokens and Smart Cards: These are like electronic ID cards for the internet. You plug them in, and they vouch for you. Super secure, but you need the physical token or card with you.
- QR Codes and Mobile Apps: Sometimes, you scan a QR code with your mobile app to get access. It’s fast and modern, but you need your phone.
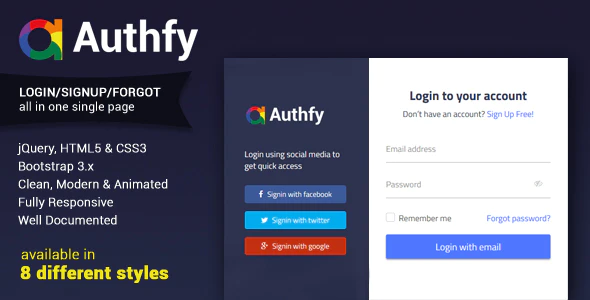
- Social Media Sign-Ins: Ever seen “Log in with Facebook” or “Sign in with Google”? It’s super convenient, but be cautious about what data you’re sharing.
How to Choose:
- Balance Security and Convenience: The more secure, the less convenient and vice versa. Consider your needs and preferences. Biometrics are super secure but not always available. Passwords are widely used but require good practices.
- Multi-Factor for Extra Armor: Combining methods, like a password and biometrics, adds an extra layer of security. It’s like having two keys to the same lock.
- Check App or Website Compatibility: Not all methods work everywhere. Some sites might offer only one option, so make sure it fits the digital lock you’re trying to open.
- User Experience Matters: The best method is the one that suits you best. It should be something you’re comfortable using regularly.
Remember, there’s no one-size-fits-all solution. So, explore your options, pick your digital key, and unlock the online world with confidence and ease!
Navigating the GDPR and JWT For Authentication: A Friendly Guide
Are you curious about how GDPR and JWT authentication are the best pals in the world of data protection and privacy? Well, let’s break it down in a friendly and straightforward way.
GDPR – The Data Guardian:
GDPR stands for General Data Protection Regulation, and it’s all about safeguarding your personal data. It’s like having a superhero guardian for your private information. GDPR ensures that companies and organizations handle your data with the utmost care and respect.
JWT Authentication – The Trusted Key:
Now, let’s talk about JWT authentication. It’s like the key to your digital castle, but it’s even more than that. It allows you to move through the digital world seamlessly, without constantly re-entering your credentials.
The Beautiful Friendship:
GDPR and JWT authentication work together like a dynamic duo. GDPR requires companies to protect your data, and JWT authentication is one way they can do that. By using JWT tokens, businesses can securely manage user identities without exposing sensitive information.
Why It Matters:
- Privacy Assurance: GDPR ensures that your data is handled with care, and JWT authentication adds an extra layer of protection when you access online services.
- Compliance: Companies that deal with your data must comply with GDPR. Using JWT authentication is one way they can meet those compliance requirements while providing a smooth user experience.
- User Control: Both GDPR and JWT authentication give you more control over your data. You decide who has access and when.
So, next time you log into a website or app, remember that GDPR and JWT authentication are there to make sure your data stays safe and your experience stays smooth. It’s like having your digital cake and eating it too!
In conclusion, the JWT token for authentication, our trusty digital key, makes online life more secure and user-friendly. With its tamper-proof, efficient, and versatile nature, it’s the ultimate sidekick in the world of digital authentication.